Fix Usage event when a volume in allocated state is deleted#5901
Conversation
|
@SadiJr your solution is great if it works. I does look a bit counter intuitive however; |
|
@DaanHoogland, when a volume is created, ACS generates a record in the table This is the normal flow, however, when a volume in state |
|
ok, thanks @SadiJr , I got that. But is removing the ALLOCATED state from the list safe? That all said, your code looks good and testing will have to prove it ;) |
|
@DaanHoogland a more complex explanation:
PS: I'm not sure I was clear in my answer. If you have any questions or suggestions, just let me know :) |
There was a problem hiding this comment.
@SadiJr thanks for the PR.
I think that I understood the whole situation and, hopefully, I can also extend your (@SadiJr) explanation to @DaanHoogland. Please let me know if I am wrong.
So, the main issue is that CloudStack usage requires that the Volume transits to operation succeeded after the DestroyRequest (which makes sense, so it ensures there would be no garbage in a storage pool in case something goes wrong with the deletion process).
Easier to see this needed action when checking the Volume state machine:
s_fsm.addTransition(new StateMachine2.Transition<State, Event>(Destroy, Event.OperationSucceeded, Destroy, Arrays.asList(new StateMachine2.Transition.Impact[]{StateMachine2.Transition.Impact.USAGE})));
So indeed, the state machine transition from Destroy via the event OperationSucceeded impacts also in the usage new StateMachine2.Transition.Impact[]{StateMachine2.Transition.Impact.USAGE}))
Any volume in the "Allocated" State (The volume is allocated but has not been created yet) is simply an entry in the DB, so no reason to "not have" the Volume.Event.OperationSucceeded.
With that said, your code is LGTM.
|
@blueorangutan package |
|
@nvazquez a Jenkins job has been kicked to build packages. I'll keep you posted as I make progress. |
|
Packaging result: ✔️ el7 ✔️ el8 ✔️ debian ✔️ suse15. SL-JID 2658 |
|
@blueorangutan test |
|
@nvazquez a Trillian-Jenkins test job (centos7 mgmt + kvm-centos7) has been kicked to run smoke tests |
|
Trillian test result (tid-3392)
|
Description
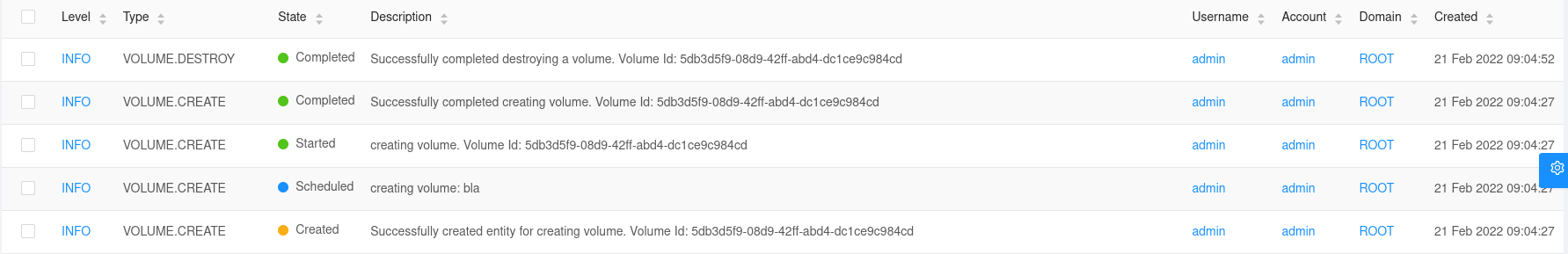
When deleting a volume in
allocatedstate, via API deleteVolume, no Usage event is generated, which causes an inconsistency in the Usage Server. Therefore, the volume appears as never deleted/destroyed.Types of changes
Feature/Enhancement Scale or Bug Severity
Bug Severity
How Has This Been Tested?
It's tested in a local lab:
cloud_usageDB, the new volumes appears only with theVOLUME.CREATEevent. NoVOLUME.DELETEevent is handled, which causes the volume to be never "deleted/destroyed" in the usage system.allocatedstate, theVOLUME.DELETEusage event is correctly handled.